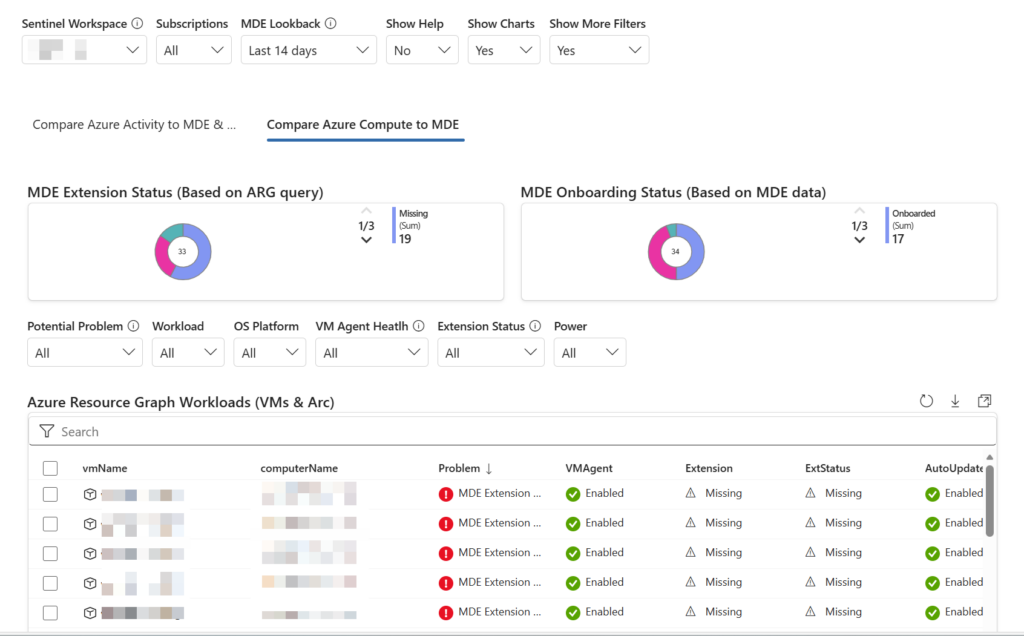
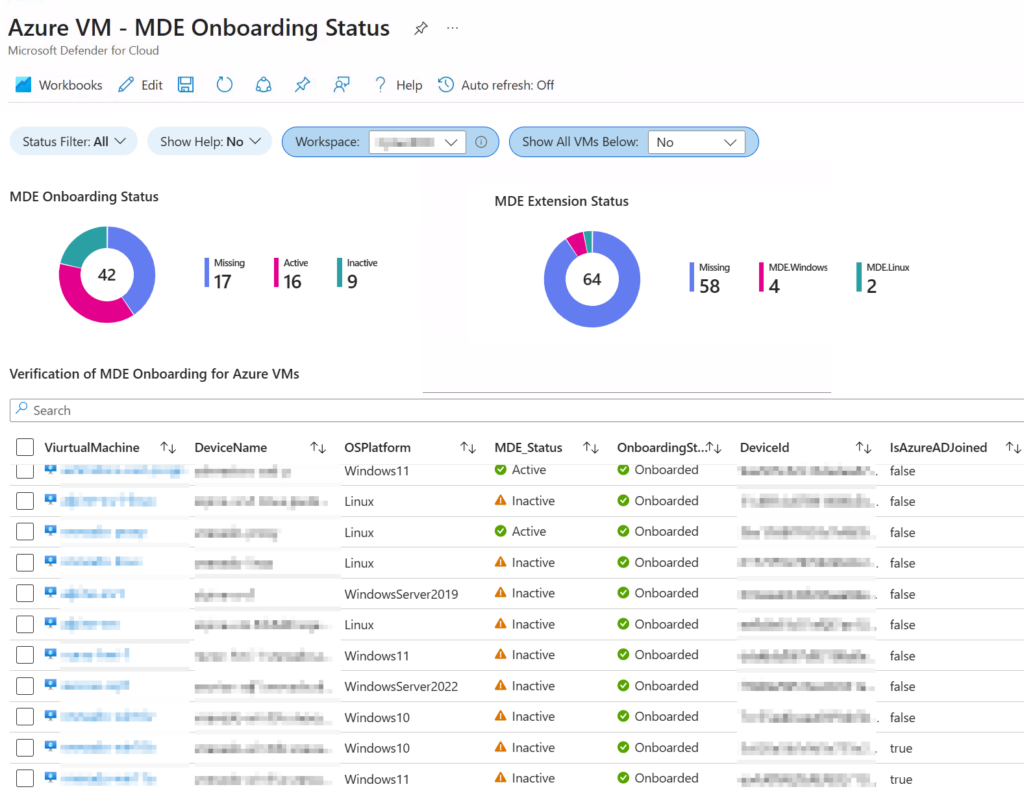
I recently built an Azure Monitor workbook to help customers who are struggling to verify that all Azure virtual machines are fully onboarded to Microsoft Defender for Endpoint (MDE).
Repo: AndrewBlumhardt/workbooks
In theory, this should be straightforward. When Defender for Servers is enabled as part of Microsoft Defender for Cloud, Azure VMs are automatically onboarded to MDE. In practice, that process can break down in several ways. Guest agent issues, extension failures, subscription misconfiguration, or prior direct onboarding methods can all lead to situations where a VM appears healthy in one view but is missing MDE protection in another.
The impact is more than cosmetic. When onboarding fails, customers lose visibility, advanced detection capabilities, and parts of the value they are paying for with Defender for Servers. More importantly, workloads that appear protected may not be generating endpoint telemetry at all.
This workbook was designed to make that gap visible. It correlates Azure activity data with MDE device records to show which VMs are actively running and whether they are properly onboarded. It also includes guidance for interpreting common failure patterns and basic remediation steps to help teams move from detection to resolution more quickly.
The goal is not to replace existing portal views, but to provide a practical validation tool that works at scale and highlights issues that are otherwise easy to miss.
The workbook template, documentation, and example screenshot are available in the GitHub repository for anyone who wants to use or adapt it for their environment. AndrewBlumhardt/workbooks
Feb 2026 Updates
I’ve made several meaningful updates to the Azure VM MDE verification workbook since the original post, focused on making it more accurate, easier to use, and more practical in real environments. The latest version improves how Azure activity data is correlated with Defender device telemetry so it’s much easier to spot machines that look fine in Azure but are not actually protected in MDE. I also expanded the help guidance based on real troubleshooting scenarios, including clearer direction for identifying guest agent problems, onboarding conflicts, and cases where Defender for Servers configuration is the root cause.
The GitHub repo has been refreshed as well with the newest workbook template, updated documentation, and cleaner import steps so you can deploy or adapt it quickly in your own tenant. The goal is still the same as when I first shared it: give security teams a fast, reliable way to validate coverage across subscriptions without chasing individual VMs. If you already pulled an earlier version, it’s worth grabbing the latest build since the detection logic and guidance have both improved quite a bit.